Check the docs before asking a question: https://docs.abp.io/en/commercial/latest/ Check the samples, to see the basic tasks: https://docs.abp.io/en/commercial/latest/samples/index The exact solution to your question may have been answered before, please use the search on the homepage.
- ABP Framework version: v3.3.2
- UI type: Angular
- DB provider: EF Core
- Tiered (MVC) or Identity Server Separated (Angular): yes
- Exception message and stack trace:
- Steps to reproduce the issue:
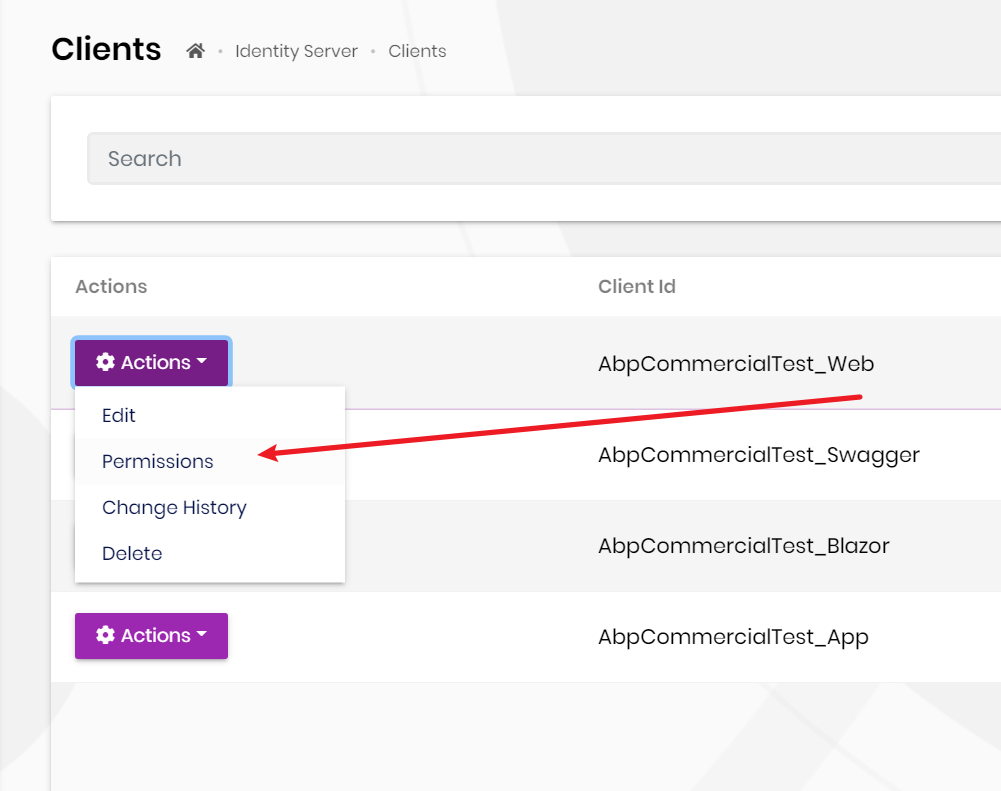
Hi, We have created a identity server client with grant type = client_credentials to let another application retrieving our data, now we create another tenant but dont know how to grant access for this client to access new tenant data, the "Identity Server -> Clients" does not appear if I login as tenant admin. any help would be much appreciated.
6 Answer(s)
-
0
-
0
Hi @maliming, thanks for your reply.
As I mentioned above, the Identity Server -> Client does not appear when I logged in as tenant admin, so I could not grant permission to this client on the tenant level.
Is there a way to achieve it without coding?
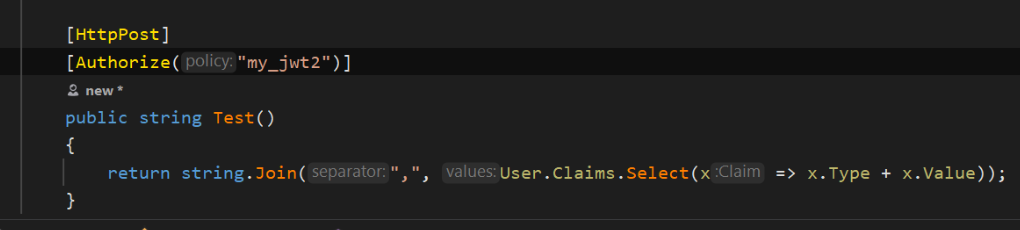
If we have to do the coding, the application service requires one policy for authenticated users:
[RemoteService(IsEnabled = false)] [Authorize(testingAppPermissions.TestingTenancies.Default)] public class TestingTenancyAppService : ApplicationService, ITestingTenancyAppServicethe Authorize does not allow multiple policies, how to combine it with the custom policy for identity server client?
-
0
As I mentioned above, the Identity Server -> Client does not appear when I logged in as tenant admin, so I could not grant permission to this client on the tenant level.
The relevant entities of the identity server are not multi-tenant. You can only grant permissions to client on Host level.
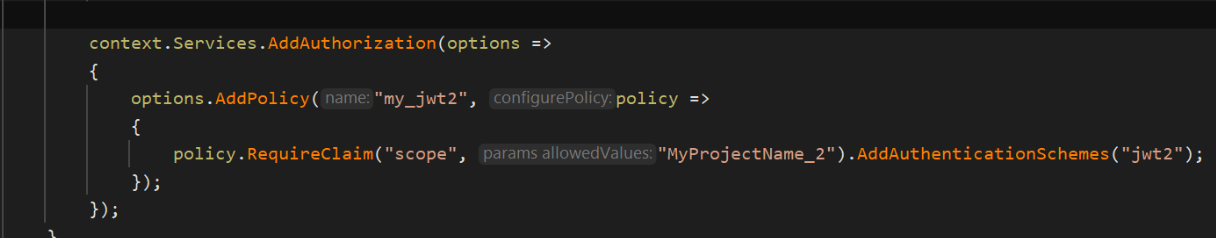
the Authorize does not allow multiple policies, how to combine it with the custom policy for identity server client?
context.Services.AddAuthorization(options => { options.AddPolicy("YourPolicy", policy => policy.AddRequirements(new IAuthorizationRequirement[] { new Volo.Abp.Authorization.PermissionRequirement("Abp Permission Name 1"), new Volo.Abp.Authorization.PermissionRequirement("Abp Permission Name 2") })); }); [Authorize("YourPolicy")] public class TestingTenancyAppService : ApplicationService, ITestingTenancyAppServicehttps://docs.microsoft.com/en-us/aspnet/core/security/authorization/policies?view=aspnetcore-5.0
-
0
Hi @maliming, thanks for your prompt reply.
With the coding solution, we need to add a quite number of policies and update the Authorize("new_policy") for all the AppService that we want to share the tenant data. If we introduce a new table then need to update code again.
can we achieve it without coding, or do we have any other alternative solution to configure permission to let another party securely retrieve/update our tenant data without using IS4 client?
-
0
hi
I don't know a solution that without coding.
You can take a look at this https://docs.microsoft.com/en-us/aspnet/core/security/authorization/iauthorizationpolicyprovider?view=aspnetcore-5.0
-
0
This question has been automatically marked as stale because it has not had recent activity.