"raif" की गतिविधियाँ
OU and roles are mainly used to organize permissions and your module should only need to the permission system dependency (it already has). These details are internals of the Identity module.
I think permission system dependency looks enough if you are building "policy based" authorization but not "row level" authorization.
Let's assume use case where we are adding query filters according users organization unit detail. We may want to the user access more or less data according to their hierarchy in the organizational unit. Policy authorized one end point should return all organizational units lookup values for assignment.
Let's define interface for this;
public interface IHasAccessControl
{
public string OwnerId { get; }
public string OrganizationId { get; }
}
Implement interface to the Aggregate Root
public class Project : AuditedAggregateRoot<Guid>, IMultiTenant, IHasAccessControl
{
public virtual string Name { get; protected set; }
// ...
public virtual Guid? TenantId { get; protected set; }
public virtual string OwnerId { get; protected set; }
public virtual string OrganizationId { get; protected set; }
public virtual void SetOwnerId([NotNull] string ownerId)
{
}
public virtual void SetOrganizationId([NotNull] string organizationId)
{
}
}
Let's add organization id information to the token.
public class OrganizationUnitPrincipalContributor : IAbpClaimsPrincipalContributor, ITransientDependency
{
public async Task ContributeAsync(AbpClaimsPrincipalContributorContext context)
{
var identity = context.ClaimsPrincipal.Identities.FirstOrDefault();
var userId = identity?.FindUserId();
if (userId.HasValue)
{
var userService = context.ServiceProvider.GetRequiredService< IdentityUserManager >();
var user = await userService.FindByIdAsync(userId.ToString());
if (user != null)
{
user.OrganizationUnits
.Select(u => u.OrganizationUnitId).ToList()
.ForEach(unit => identity.AddClaim(new Claim(type: "organization_unit", value: unit.ToString())));
}
}
}
}
Add short cut for identityServer (https://github.com/abpframework/abp/pull/7998)
Configure<AbpClaimsServiceOptions>(options =>
{
options.RequestedClaims.AddRange(new[] { "organization_unit" });
});
Create extension for CurrentUser in order to get OrganizationIds from token.
public static class CurrentUserExtensions
{
public static string[] GetOrganizationUnits(this ICurrentUser currentUser)
{
Claim[] claims = currentUser.FindClaims("organization_unit");
return claims.Select(c => c.Value).ToArray();
}
}
Add query filters for EF Core
protected override bool ShouldFilterEntity< TEntity >(IMutableEntityType entityType)
{
if (typeof(IHasAccessControl).IsAssignableFrom(typeof(TEntity)))
{
return true;
}
return base.ShouldFilterEntity< TEntity >(entityType);
}
protected override Expression< Func< TEntity, bool > > CreateFilterExpression< TEntity >()
{
var expression = base.CreateFilterExpression< TEntity >();
if (typeof(IHasAccessControl).IsAssignableFrom(typeof(TEntity)))
{
Expression< Func < TEntity, bool > > hasAccessControlFilter = e => CurrentUser.GetOrganizationUnits().Contains(EF.Property< string >(e, "OrganizationId")) || CurrentUser.Id == (EF.Property< string >(e, "OwnerId"));
expression = expression == null ? hasAccessControlFilter : CombineExpressions(expression, hasAccessControlFilter);
}
return expression;
}
Let suppose we have microservices A and B. A for identity, auditing, saas etc, basic IT needs Where B is business microservice.
After creating a new "project" object in microservice B, I want to assign it to a specific person or a specific organizational unit. (see global filter implementation)
So we needed lookup values for organization units (it can be logins, tokens, roles, claims for another use cases)
Information exchange between A and B can be
- Synchronous
- Asynchronous (in this specific case data can flow one way)
Again let assume that we would like keep asynchronous communication where we were using UserEtos
So, every time the user is updated in microservice A, I want to update the user information in microservice B via distributed events.
However UserEto's doesn't carry information about
- Claims
- Roles
- Logins
- Tokens
- Organization Units
So how can we access asynchronously the above information about the user ?
UserLookupService from Volo.Abp.Users package only forces IUser interface which is doesn't force claims, roles, tokens, ou etc..
public abstract class UserLookupService<TUser, TUserRepository> : IUserLookupService<TUser>, ITransientDependency where TUser : class, IUser where TUserRepository : IUserRepository<TUser>
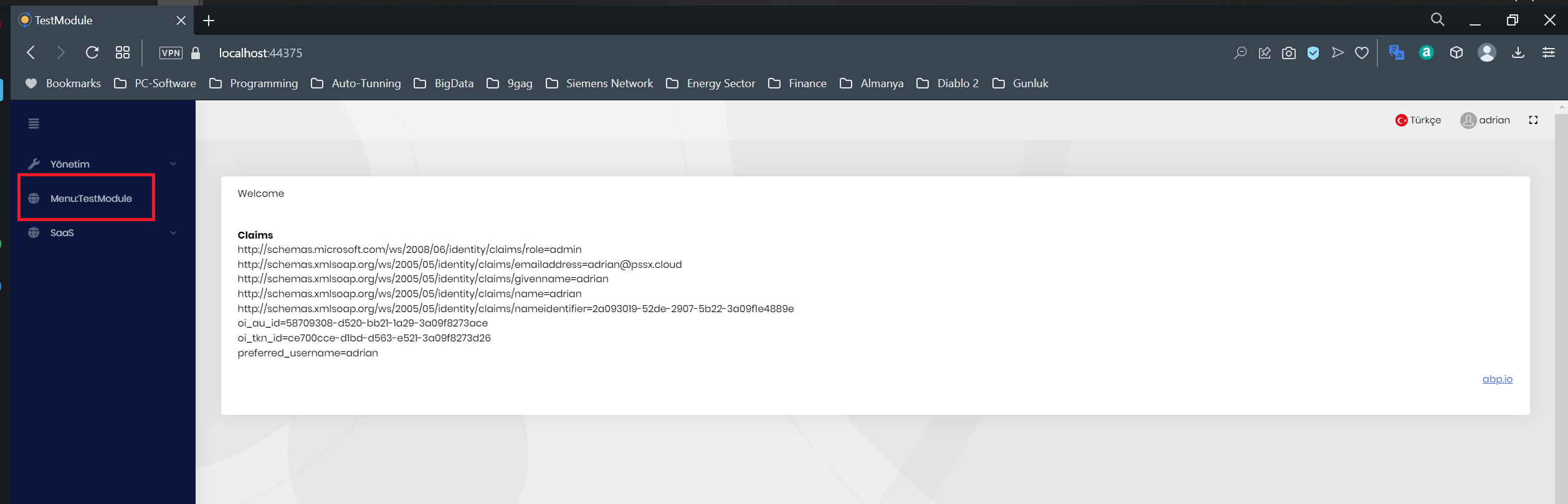
- ABP Framework version: v7.0.2
- UI type: MVC
- DB provider: EF Core
- Tiered (MVC) or Identity Server Separated (Angular): yes
- Steps to reproduce the issue:"
- Create a new module from template
- Disable redis by updating appsettings.json
- Use Web.Host for ui
- Wait 30 min
 Menu items are going to disappear, most possible due to expired token.
Menu items are going to disappear, most possible due to expired token.
Is it related with https://support.abp.io/QA/Questions/4677/User-lost-credentials-after-30min-without-activity or https://github.com/abpframework/abp/issues/14068
- ABP Framework version: v7.0.2
- UI type: MVC
- DB provider: EF Core
- Tiered (MVC) or Identity Server Separated (Angular): yes
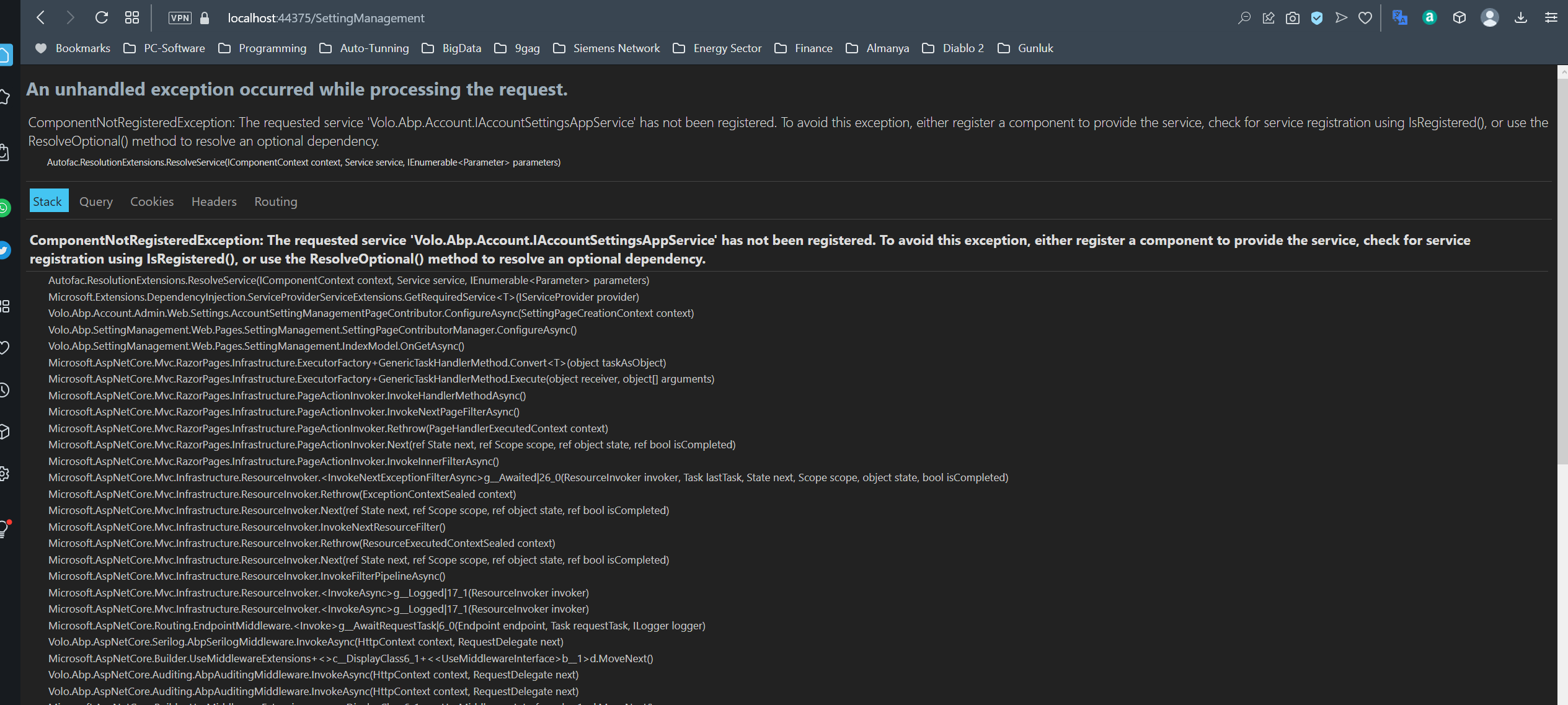
- Exception message and stack trace: *Autofac.Core.Registration.ComponentNotRegisteredException: The requested service 'Volo.Abp.Account.IAccountSettingsAppService' has not been registered. To avoid this exception, either register a component to provide the service, check for service registration using IsRegistered(), or use the ResolveOptional() method to resolve an optional dependency. at Autofac.ResolutionExtensions.ResolveService(IComponentContext context, Service service, IEnumerable`1 parameters) at Microsoft.Extensions.DependencyInjection.ServiceProviderServiceExtensions.GetRequiredService[T](IServiceProvider provider) at Volo.Abp.Account.Admin.Web.Settings.AccountSettingManagementPageContributor.ConfigureAsync(SettingPageCreationContext context) at Volo.Abp.SettingManagement.Web.Pages.SettingManagement.SettingPageContributorManager.ConfigureAsync() at Volo.Abp.SettingManagement.Web.Pages.SettingManagement.IndexModel.OnGetAsync() at Microsoft.AspNetCore.Mvc.RazorPages.Infrastructure.ExecutorFactory.GenericTaskHandlerMethod.Convert[T](Object taskAsObject) at Microsoft.AspNetCore.Mvc.RazorPages.Infrastructure.ExecutorFactory.GenericTaskHandlerMethod.Execute(Object receiver, Object[] arguments) at Microsoft.AspNetCore.Mvc.RazorPages.Infrastructure.PageActionInvoker.InvokeHandlerMethodAsync() at Microsoft.AspNetCore.Mvc.RazorPages.Infrastructure.PageActionInvoker.InvokeNextPageFilterAsync() at Microsoft.AspNetCore.Mvc.RazorPages.Infrastructure.PageActionInvoker.Rethrow(PageHandlerExecutedContext context) at Microsoft.AspNetCore.Mvc.RazorPages.Infrastructure.PageActionInvoker.Next(State& next, Scope& scope, Object& state, Boolean& isCompleted) at Microsoft.AspNetCore.Mvc.RazorPages.Infrastructure.PageActionInvoker.InvokeInnerFilterAsync() at Microsoft.AspNetCore.Mvc.Infrastructure.ResourceInvoker.
- Steps to reproduce the issue:
- Create a new module from template
- Login with admin user
- Hit the settings
Most possible it is due to missing Volo.Abp.Account.Pro.Admin.HttpApi.Client package at .Web.Host template
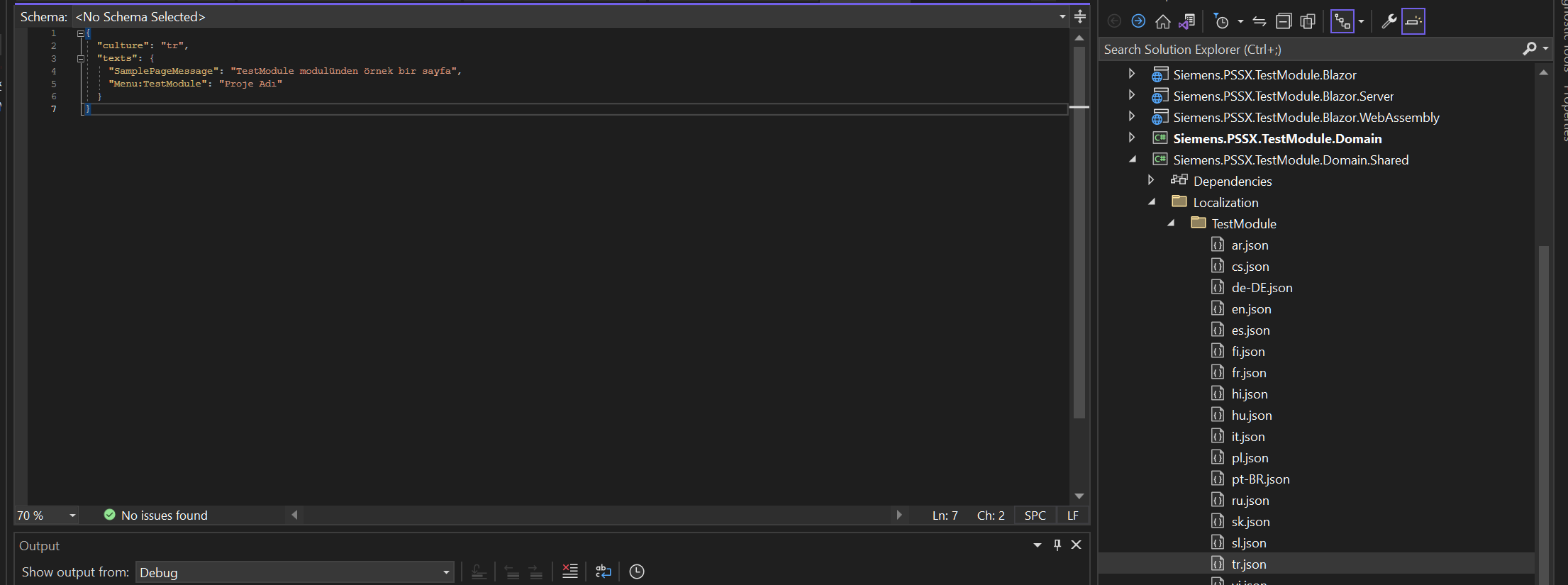
- ABP Framework version: v7.0.2
- UI type: MVC
- DB provider: EF Core
- Tiered (MVC) or Identity Server Separated (Angular): yes
- Steps to reproduce the issue:"
- Create module from the template
- For the sake of example modify menu item
private static ApplicationMenuItem AddModuleMenuItem(MenuConfigurationContext context)
{
var l = context.GetLocalizer<TestModuleResource>();
var moduleMenu = new ApplicationMenuItem(
TestModuleMenus.Prefix,
displayName: l["Menu:TestModule"],
"~/TestModule",
icon: "fa fa-globe");
//Add main menu items.
context.Menu.Items.AddIfNotContains(moduleMenu);
return moduleMenu;
}
I believe that it is related with virtual file configuration of the Web.Host template
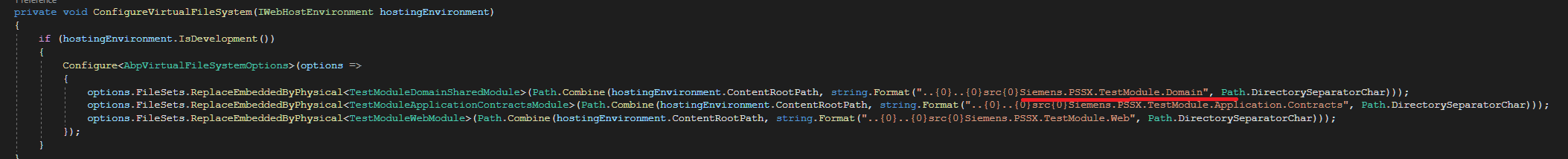 File path needs to be Domain.Shared not Domain
File path needs to be Domain.Shared not Domain
Also sent entire log via e-mail;
AuthServer;
2023-03-16 12:53:09.035 +01:00 [INF] Executing endpoint 'Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.AbpApplicationConfigurationController.GetAsync (Volo.Abp.AspNetCore.Mvc)' 2023-03-16 12:53:09.036 +01:00 [INF] Route matched with {area = "abp", action = "Get", controller = "AbpApplicationConfiguration", page = ""}. Executing controller action with signature System.Threading.Tasks.Task`1[Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.ApplicationConfigurationDto] GetAsync(Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.ApplicationConfigurationRequestOptions) on controller Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.AbpApplicationConfigurationController (Volo.Abp.AspNetCore.Mvc). 2023-03-16 12:53:09.063 +01:00 [INF] Executing action method Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.AbpApplicationConfigurationController.GetAsync (Volo.Abp.AspNetCore.Mvc) - Validation state: "Valid" 2023-03-16 12:53:09.065 +01:00 [DBG] Executing AbpApplicationConfigurationAppService.GetAsync()... 2023-03-16 12:53:09.096 +01:00 [DBG] Executed AbpApplicationConfigurationAppService.GetAsync(). 2023-03-16 12:53:09.097 +01:00 [INF] Executed action method Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.AbpApplicationConfigurationController.GetAsync (Volo.Abp.AspNetCore.Mvc), returned result Microsoft.AspNetCore.Mvc.ObjectResult in 33.3081ms. 2023-03-16 12:53:09.097 +01:00 [DBG] Added 0 entity changes to the current audit log 2023-03-16 12:53:09.098 +01:00 [DBG] Added 0 entity changes to the current audit log 2023-03-16 12:53:09.099 +01:00 [INF] Executing ObjectResult, writing value of type 'Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.ApplicationConfigurationDto'. 2023-03-16 12:53:09.101 +01:00 [INF] Executed action Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.AbpApplicationConfigurationController.GetAsync (Volo.Abp.AspNetCore.Mvc) in 65.0083ms 2023-03-16 12:53:09.101 +01:00 [INF] Executed endpoint 'Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.AbpApplicationConfigurationController.GetAsync (Volo.Abp.AspNetCore.Mvc)' 2023-03-16 12:53:09.101 +01:00 [INF] Request finished HTTP/1.1 GET https://localhost:44374/api/abp/application-configuration?IncludeLocalizationResources=False&api-version=1.0 - - - 200 - application/json;+charset=utf-8 68.7130ms 2023-03-16 12:53:09.168 +01:00 [INF] Request starting HTTP/1.1 GET https://localhost:44374/api/abp/application-localization?CultureName=en&OnlyDynamics=True&api-version=1.0 - - 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessRequestContext was successfully processed by OpenIddict.Validation.AspNetCore.OpenIddictValidationAspNetCoreHandlers+ResolveRequestUri. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Server.OpenIddictServerEvents+ProcessRequestContext was successfully processed by OpenIddict.Server.AspNetCore.OpenIddictServerAspNetCoreHandlers+ResolveRequestUri. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Server.OpenIddictServerEvents+ProcessRequestContext was successfully processed by OpenIddict.Server.OpenIddictServerHandlers+InferEndpointType. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Server.OpenIddictServerEvents+ProcessRequestContext was successfully processed by Volo.Abp.Account.Web.Pages.Account.OpenIddictImpersonateInferEndpointType. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Server.OpenIddictServerEvents+ProcessRequestContext was successfully processed by OpenIddict.Server.AspNetCore.OpenIddictServerAspNetCoreHandlers+ValidateTransportSecurityRequirement. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Server.OpenIddictServerEvents+ProcessRequestContext was successfully processed by OpenIddict.Server.AspNetCore.OpenIddictServerAspNetCoreHandlers+ValidateHostHeader. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.AspNetCore.OpenIddictValidationAspNetCoreHandlers+ValidateHostHeader. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+ResolveServerConfiguration. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+EvaluateValidatedTokens. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.AspNetCore.OpenIddictValidationAspNetCoreHandlers+ExtractAccessTokenFromAuthorizationHeader. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.AspNetCore.OpenIddictValidationAspNetCoreHandlers+ExtractAccessTokenFromBodyForm. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.AspNetCore.OpenIddictValidationAspNetCoreHandlers+ExtractAccessTokenFromQueryString. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+ValidateRequiredTokens. 2023-03-16 12:53:09.169 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ValidateTokenContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+Protection+ResolveTokenValidationParameters. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ValidateTokenContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+Protection+ValidateIdentityModelToken. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ValidateTokenContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+Protection+NormalizeScopeClaims. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ValidateTokenContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+Protection+MapInternalClaims. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ValidateTokenContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+Protection+ValidatePrincipal. 2023-03-16 12:53:09.170 +01:00 [INF] The authentication demand was rejected because the token was expired. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ValidateTokenContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+Protection+ValidateExpirationDate. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ValidateTokenContext was marked as rejected by OpenIddict.Validation.OpenIddictValidationHandlers+Protection+ValidateExpirationDate. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was successfully processed by OpenIddict.Validation.OpenIddictValidationHandlers+ValidateAccessToken. 2023-03-16 12:53:09.170 +01:00 [DBG] The event OpenIddict.Validation.OpenIddictValidationEvents+ProcessAuthenticationContext was marked as rejected by OpenIddict.Validation.OpenIddictValidationHandlers+ValidateAccessToken. 2023-03-16 12:53:09.170 +01:00 [INF] OpenIddict.Validation.AspNetCore was not authenticated. Failure message: An error occurred while authenticating the current request. 2023-03-16 12:53:09.170 +01:00 [INF] OpenIddict.Validation.AspNetCore was not authenticated. Failure message: An error occurred while authenticating the current request. 2023-03-16 12:53:09.171 +01:00 [INF] Executing endpoint 'Volo.Abp.AspNetCore.Mvc.ApplicationConfigurations.AbpApplicationLocalizationController.GetAsync (Volo.Abp.AspNetCore.Mvc)'
Api Host;
2023-03-16 12:53:06.141 +01:00 [DBG] Batch acquisition of 0 triggers
2023-03-16 12:53:09.691 +01:00 [INF] Request starting HTTP/1.1 GET https://localhost:44319/api/project-planning/base-models/properties?Sorting=baseModel.name+asc&SkipCount=0&MaxResultCount=10&api-version=1.0 - -
2023-03-16 12:53:09.712 +01:00 [DBG] Acquiring a lock on 3b2efba2d4d943c6be4c79e83d238a72
2023-03-16 12:53:09.713 +01:00 [DBG] Lock acquired on 3b2efba2d4d943c6be4c79e83d238a72
2023-03-16 12:53:09.811 +01:00 [DBG] Found 0 workflows with correlation ID 3b2efba2d4d943c6be4c79e83d238a72
2023-03-16 12:53:09.811 +01:00 [DBG] Triggering workflows using HttpEndpoint
2023-03-16 12:53:09.860 +01:00 [INF] Failed to validate the token.
Microsoft.IdentityModel.Tokens.SecurityTokenExpiredException: IDX10223: Lifetime validation failed. The token is expired. ValidTo: '3/16/2023 10:33:46 AM', Current time: '3/16/2023 11:53:09 AM'.
at Microsoft.IdentityModel.Tokens.Validators.ValidateLifetime(Nullable1 notBefore, Nullable1 expires, SecurityToken securityToken, TokenValidationParameters validationParameters)
at System.IdentityModel.Tokens.Jwt.JwtSecurityTokenHandler.ValidateLifetime(Nullable1 notBefore, Nullable1 expires, JwtSecurityToken jwtToken, TokenValidationParameters validationParameters)
at System.IdentityModel.Tokens.Jwt.JwtSecurityTokenHandler.ValidateTokenPayload(JwtSecurityToken jwtToken, TokenValidationParameters validationParameters, BaseConfiguration configuration)
at System.IdentityModel.Tokens.Jwt.JwtSecurityTokenHandler.ValidateJWS(String token, TokenValidationParameters validationParameters, BaseConfiguration currentConfiguration, SecurityToken& signatureValidatedToken, ExceptionDispatchInfo& exceptionThrown)
--- End of stack trace from previous location ---
at System.IdentityModel.Tokens.Jwt.JwtSecurityTokenHandler.ValidateToken(String token, JwtSecurityToken outerToken, TokenValidationParameters validationParameters, SecurityToken& signatureValidatedToken)
at System.IdentityModel.Tokens.Jwt.JwtSecurityTokenHandler.ValidateToken(String token, TokenValidationParameters validationParameters, SecurityToken& validatedToken)
at Microsoft.AspNetCore.Authentication.JwtBearer.JwtBearerHandler.HandleAuthenticateAsync()
2023-03-16 12:53:09.864 +01:00 [INF] Bearer was not authenticated. Failure message: IDX10223: Lifetime validation failed. The token is expired. ValidTo: '3/16/2023 10:33:46 AM', Current time: '3/16/2023 11:53:09 AM'.
2023-03-16 12:53:09.919 +01:00 [INF] Executing endpoint 'Siemens.PSSX.ProjectPlanning.BaseModels.v1.BaseModelController.GetListWithNavigationPropertiesAsync (Siemens.PSSX.ProjectPlanning.HttpApi)'
2023-03-16 12:53:09.922 +01:00 [INF] Route matched with {controller = "Base Models", action = "GetListWithNavigationProperties", area = "", page = ""}. Executing controller action with signature System.Threading.Tasks.Task1[Volo.Abp.Application.Dtos.PagedResultDto1[Siemens.PSSX.ProjectPlanning.BaseModels.v1.Dtos.BaseModelWithNavigationPropertiesDto]] GetListWithNavigationPropertiesAsync(Siemens.PSSX.ProjectPlanning.BaseModels.v1.Dtos.GetBaseModelWithNavigationPropertiesInput) on controller Siemens.PSSX.ProjectPlanning.BaseModels.v1.BaseModelController (Siemens.PSSX.ProjectPlanning.HttpApi).
2023-03-16 12:53:10.006 +01:00 [INF] Executing action method Siemens.PSSX.ProjectPlanning.BaseModels.v1.BaseModelController.GetListWithNavigationPropertiesAsync (Siemens.PSSX.ProjectPlanning.HttpApi) - Validation state: "Valid"
2023-03-16 12:53:10.027 +01:00 [INF] Authorization failed. These requirements were not met:
PermissionRequirement: ProjectPlanning.BaseModel
2023-03-16 12:53:10.166 +01:00 [WRN] ---------- RemoteServiceErrorInfo ----------
{
"code": "Volo.Authorization:010001",
"message": "Authorization failed! Given policy has not granted.",
"details": null,
"data": {},
"validationErrors": null
}
- ABP Framework version: v7.0.2
- UI type: MVC
- DB provider: EF Core
- Tiered (MVC) or Identity Server Separated (Angular): yes
Hello, We can load module classes as plug-ins without adding reference to project. The relevant explanation is https://docs.abp.io/en/abp/latest/PlugIn-Modules located at here.
Where should we define MyPlugInDemoWebModule class in this example?
using Microsoft.AspNetCore.Builder;
using Microsoft.Extensions.DependencyInjection;
using Volo.Abp.Modularity.PlugIns;
namespace MyPlugInDemo.Web
{
public class Startup
{
public void ConfigureServices(IServiceCollection services)
{
services.AddApplication<MyPlugInDemoWebModule>(options =>
{
options.PlugInSources.AddFolder(@"D:\Temp\MyPlugIns");
});
}
public void Configure(IApplicationBuilder app)
{
app.InitializeApplication();
}
}
}
This sample code does not seem updated.
Can we replace ConfigureServices(IServiceCollection services) part with
public override void ConfigureServices(ServiceConfigurationContext context)
{
}
and Configure(IApplicationBuilder app) part with
public override void OnApplicationInitialization(ApplicationInitializationContext context)
{
var app = context.GetApplicationBuilder();
app.InitializeApplication();
}
More importantly, Can you share an example where we consume a service in a project that we did add as reference
For example, I want to call MyService : IMyService, ITransientDependency that we created in the plug-in
- ABP Framework version: v7.3.2
- UI Type: MVC
- Database System: EF Core SQL Server
- Tiered (for MVC) or Auth Server Separated (for Angular): yes
context.Services.AddAuthentication()
//.AddAbpOpenIdConnect("myAuthSchema", "myAuth AD", options =>
.AddOpenIdConnect("myAuthSchema", "myAuth AD", options =>
{
options.Authority = configuration["AzureAd:Authority"].EnsureEndsWith('/') + configuration["AzureAd:TenantId"].EnsureEndsWith('/') + "v2.0".TrimEnd('/');
options.MetadataAddress = configuration["AzureAd:MetadataAddress"].EnsureEndsWith('/') + configuration["AzureAd:TenantId"].EnsureEndsWith('/') + "v2.0".EnsureEndsWith('/') + ".well-known/openid-configuration";
options.ResponseType = OpenIdConnectResponseType.CodeIdToken;
options.ClientId = configuration["AzureAd:ClientId"];
options.ClientSecret = configuration["AzureAd:ClientSecret"];
options.UsePkce = true;
options.GetClaimsFromUserInfoEndpoint = true;
options.TokenValidationParameters = new TokenValidationParameters()
{
ValidateIssuer = true,
};
options.TokenValidationParameters.ValidIssuers = new[]
{
configuration["AzureAd:MetadataAddress"],
configuration["AzureAd:Authority"]
};
options.Scope.Add("openid");
options.Scope.Add("profile");
options.Scope.Add("offline_access");
options.Scope.Add("email");
});
.WithDynamicOptions < OpenIdConnectOptions, OpenIdConnectHandler > (
"myAuthSchema",
options =>
{
options.WithProperty(x => x.ClientId);
options.WithProperty(x => x.ClientSecret, isSecret: true);
}
);
I would like to provide ClientId and ClientSecret values via Account External Provider Settings
/api/account/external-provider endpoint keeps returning only Google, Twitter and Microsoft values
I also tried to extend provider list via AbpExternalProviderOptions but no luck
context.Services.Configure < AbpExternalProviderOptions > (options =>
{
options.Definitions.Add(new ExternalProviderDefinition()
{
Name = "Test",
Properties = new List < ExternalProviderDefinitionProperty >()
});
});
What am i missing ?
Check the docs before asking a question: https://docs.abp.io/en/abp/latest/API/API-Versioning https://docs.abp.io/en/abp/7.3/UI/AspNetCore/Data-Tables
Check the samples to see the basic tasks: https://github.com/abpframework/abp-samples/tree/master/Api-Versioning [This example doesn't show how to integrate api versiong with Datatables ]
- ABP Framework version: v7.3.1
- UI Type: MVC /
- Database System: EF Core (SQL Server)
- Tiered (for MVC) or Auth Server Separated (for Angular): ye
- Exception message and full stack trace:
- Request did not specify a service API version, but multiple candidate actions were found. Candidate actions: Siemens.PSSX.Odms.Models.v130.ModelController.GetListAsync (Siemens.PSSX.Odms.HttpApi) Siemens.PSSX.Odms.Models.v131.ModelController.GetListAsync (Siemens.PSSX.Odms.HttpApi)
We have more than one version of one of our APIs.
We can easily see the versions through the Swagger interface and working as intended.
JS proxy configuration from .Web project as shown below;
(function(){
abp.utils.createNamespace(window, 'siemens.pSSX.odms.models.v130.model');
... ///
siemens.pSSX.odms.models.v130.model.getList = function(input, ajaxParams) {
var api_version = api_version ? api_version : '13.0';
return abp.ajax($.extend(true, {
url: abp.appPath + 'api/odms/models' + abp.utils.buildQueryString([{ name: 'filterText', value: input.filterText }, { name: 'name', value: input.name }, { name: 'description', value: input.description }, { name: 'serverName', value: input.serverName }, { name: 'cIMVersion', value: input.cIMVersion }, { name: 'creatorId', value: input.creatorId }, { name: 'creationTimeMin', value: input.creationTimeMin }, { name: 'creationTimeMax', value: input.creationTimeMax }, { name: 'lastModifierId', value: input.lastModifierId }, { name: 'lastModificationTimeMin', value: input.lastModificationTimeMin }, { name: 'lastModificationTimeMax', value: input.lastModificationTimeMax }, { name: 'sorting', value: input.sorting }, { name: 'skipCount', value: input.skipCount }, { name: 'maxResultCount', value: input.maxResultCount }, { name: 'api-version', value: input.api_version }]) + '',
type: 'GET'
}, ajaxParams));
};
})();
(function(){
abp.utils.createNamespace(window, 'siemens.pSSX.odms.models.v131.model');
siemens.pSSX.odms.models.v131.model.getList = function(input, ajaxParams) {
var api_version = api_version ? api_version : '13.1';
return abp.ajax($.extend(true, {
url: abp.appPath + 'api/odms/models' + abp.utils.buildQueryString([{ name: 'filterText', value: input.filterText }, { name: 'name', value: input.name }, { name: 'description', value: input.description }, { name: 'serverName', value: input.serverName }, { name: 'cIMVersion', value: input.cIMVersion }, { name: 'creatorId', value: input.creatorId }, { name: 'creationTimeMin', value: input.creationTimeMin }, { name: 'creationTimeMax', value: input.creationTimeMax }, { name: 'lastModifierId', value: input.lastModifierId }, { name: 'lastModificationTimeMin', value: input.lastModificationTimeMin }, { name: 'lastModificationTimeMax', value: input.lastModificationTimeMax }, { name: 'sorting', value: input.sorting }, { name: 'skipCount', value: input.skipCount }, { name: 'maxResultCount', value: input.maxResultCount }, { name: 'api-version', value: input.api_version }]) + '',
type: 'GET'
}, ajaxParams));
};
})();
For the sake of simplicity, two different MVC UI were designed for two different API versions.
var l = abp.localization.getResource("Odms");
var modelService = siemens.pSSX.odms.models.v130.model;
var getFilter = function () {
return {
filterText: $("#FilterText").val(),
name: $("#NameFilter").val(),
description: $("#DescriptionFilter").val(),
serverName: $("#ServerNameFilter").val(),
cIMVersion: $("#CIMVersionFilter").val(),
creatorId: $("#ServerNameFilter").val(),
creationTimeMin: $("#CreationTimeFilterMin").val(),
creationTimeMax: $("#CreationTimeFilterMax").val(),
lastModifierId: $("#ServerNameFilter").val(),
lastModificationTimeMin: $("#LastModificationTimeFilterMin").val(),
lastModificationTimeMax: $("#LastModificationTimeFilterMax").val(),
};
};
var dataTable = $("#ModelsTable").DataTable(abp.libs.datatables.normalizeConfiguration({
processing: true,
serverSide: true,
paging: true,
searching: false,
scrollX: true,
autoWidth: false,
scrollCollapse: true,
order: [[1, "asc"]],
ajax: **abp.libs.datatables.createAjax(modelService.getList, getFilter),**
columnDefs: [
{
... ///
}
]
}));
abp.libs.datatables.createAjax(modelService.getList, getFilter),
How can we specify a service API version when creating ajax ?
Log: 2023-09-18 20:21:27.944 +02:00 [INF] Request did not specify a service API version, but multiple candidate actions were found. Candidate actions: Siemens.PSSX.Odms.Models.v130.ModelController.GetListAsync (Siemens.PSSX.Odms.HttpApi) Siemens.PSSX.Odms.Models.v131.ModelController.GetListAsync (Siemens.PSSX.Odms.HttpApi)