Activities of "nhontran"
Hi maliming,
Thanks for the fix, it is working now.
But may I know why do we need the AddHangfireServer? it is not included in the documentation: https://docs.abp.io/en/abp/latest/Background-Jobs-Hangfire
Hi maliming,
No errors appear in the logs, but I noticed that there is no step for starting Hangfire:
[22:43:16 INF] Start installing Hangfire SQL objects... [22:43:16 INF] Hangfire SQL objects installed. [22:43:30 INF] Starting IdentityServer4 version 4.1.2+997a6cdd643e46cd5762b710c4ddc43574cbec2e [22:43:32 INF] Using the default authentication scheme Identity.Application for IdentityServer
Btw, I have shared the source code with you via email, could you please help us check.
Thank you.
Hi, I managed to override it already. Thanks
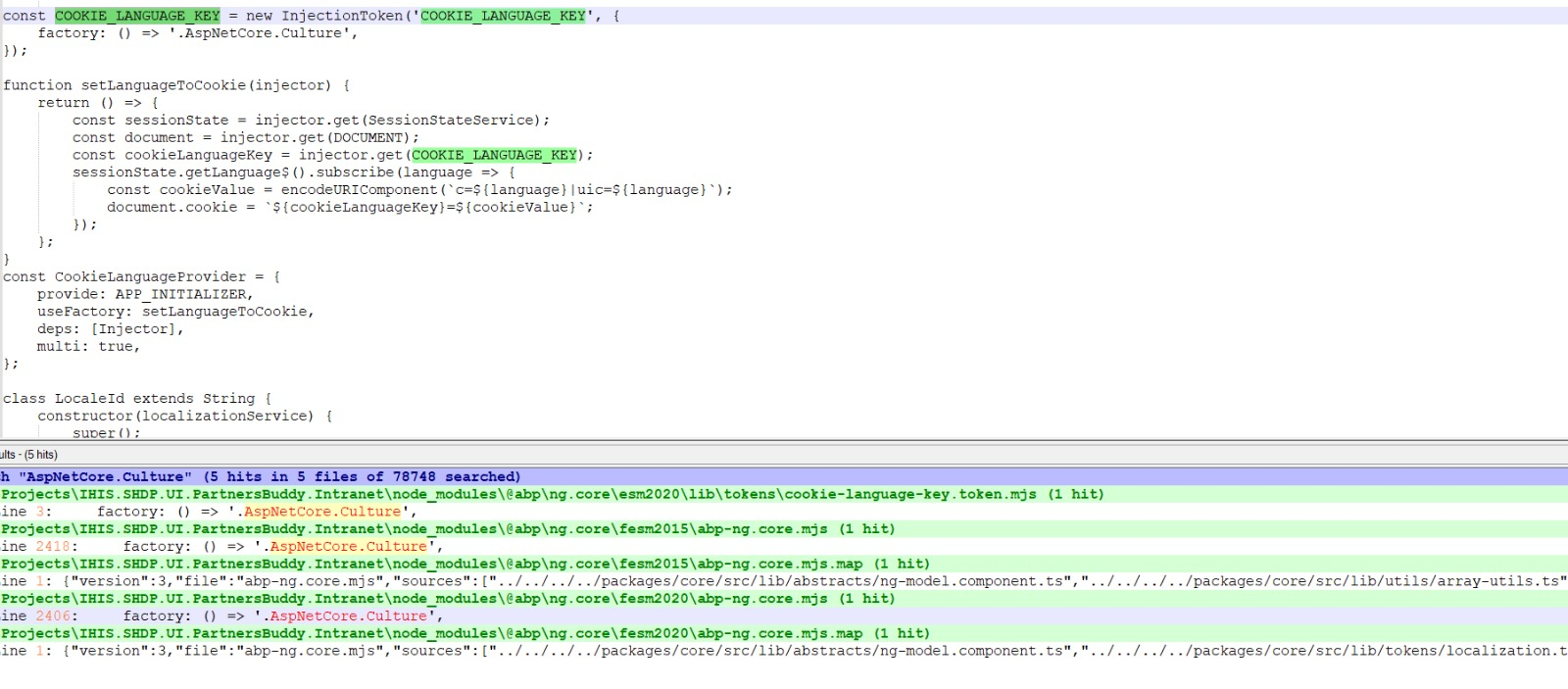
Hi @liangshiwei, sorry if my question confused you, but I want to know what cookies are created by this method in abp.js
abp.utils.setCookieValue = function (key, value, expireDate, path) {
var cookieValue = encodeURIComponent(key) + '=';
if (value) {
cookieValue = cookieValue + encodeURIComponent(value);
}
if (expireDate) {
cookieValue = cookieValue + "; expires=" + expireDate.toUTCString();
}
if (path) {
cookieValue = cookieValue + "; path=" + path;
}
document.cookie = cookieValue;
};
The purpose of using these cookies and do they contain any sensitive info?
Hi, what I want to achieve is instead of using RSA key, I want to use ECDSA key for signing credentials and encryption credentials. I find this is supported by OpenIddict in their documentation:
Encryption and signing credentials
To protect the tokens it issues, OpenIddict uses 2 types of credentials:
Signing credentials are used to protect against tampering. They can be either asymmetric (e.g a RSA or ECDSA key) or symmetric.
Encryption credentials are used to ensure the content of tokens cannot be read by malicious parties. They can be either asymmetric (e.g a RSA key) or symmetric.
but don't know why keep getting this error:
[09:54:04 DBG] An exception was thrown by OpenIddict.Server.OpenIddictServerHandlers+Protection+GenerateIdentityModelToken while handling the OpenIddict.Server.OpenIddictServerEvents+GenerateTokenContext event.
System.ArgumentNullException: IDX10000: The parameter 'privateKey' cannot be a 'null' or an empty object. (Parameter 'privateKey')
at Microsoft.IdentityModel.Tokens.EcdhKeyExchangeProvider..ctor(SecurityKey privateKey, SecurityKey publicKey, String alg, String enc)
Is there any sample code using ECDSA key instead of RSA key?
Hi @maliming, thanks, I managed to add the encryption key into JWKS URL but I got the below error when using Angular UI to login to retrieve the access token:
[09:54:04 DBG] An exception was thrown by OpenIddict.Server.OpenIddictServerHandlers+Protection+GenerateIdentityModelToken while handling the OpenIddict.Server.OpenIddictServerEvents+GenerateTokenContext event.
System.ArgumentNullException: IDX10000: The parameter 'privateKey' cannot be a 'null' or an empty object. (Parameter 'privateKey')
at Microsoft.IdentityModel.Tokens.EcdhKeyExchangeProvider..ctor(SecurityKey privateKey, SecurityKey publicKey, String alg, String enc)
Even the security key I put into EncryptingCredentials already had the private key, I have provided you the source code through email, able to help us check?
Hi @maliming, is there a way to override the handler?
Hi @maliming, I have provided the source code via email, I also attached the ECDSA cert that we use for testing.
I tried AddSigningCertificate, it does not work with ECDSA cert.
Hi @maliming, ok, let me share the full code to you.