"AlderCove" की गतिविधियाँ
that worked - thank you.
@berkansasmaz
Thanks for the solution. It worked well!
I made one minor change to the script to close the sub-menu if enter is pressed when the sub-menu is expanded:
$(function () {
var menuItems = document.querySelectorAll('li.has-drop');
Array.prototype.forEach.call(menuItems, function (el, i) {
el.querySelector('a').addEventListener("click", function (event) {
if (this.parentNode.classList.contains("has-drop")) {
if (!this.parentNode.classList.contains("open"))
this.parentNode.classList.add('open');
else
this.parentNode.classList.remove('open');
} else {
this.parentNode.className = "has-submenu";
this.setAttribute('aria-expanded', "false");
}
event.preventDefault();
return false;
});
});
});
@gterdem,
Thank you for the additional details.
I wasn't understanding how to trigger the login flow from the start and thought there was something complex that needed to be done!
I have modified the page logic to show a button with a link to the public website (which is parsed from the model return url).
Upon returning to the website, the user must log in to restart the login flow.
It's one extra step, but will resolve the issue until a more permanent solution is implemented.
I appreciate the detailed response.
Can you please let me know what I need to change to update the button to trigger the login workflow from the start again?
Thank you.
Hi, any update on this?
We are going live soon and this is a critical issue for us.
Thanks
Shared with info@abp.io
Hi - any thoughts?
I created a new project with abp suite and was able to isolate the issue a little better.
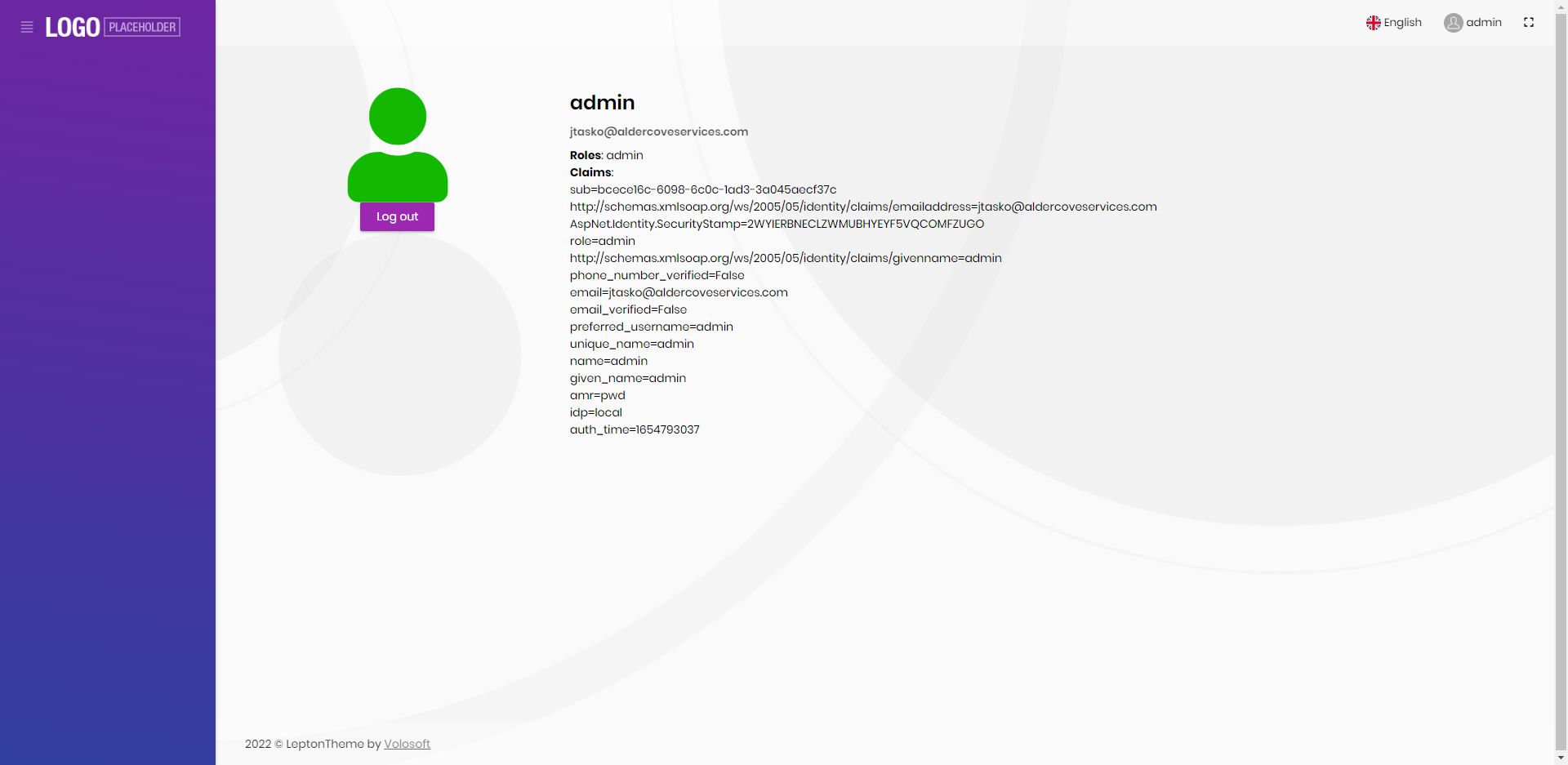
ABP Framework version: v5.1.4 UI type: Angular DB provider: EF Core Tiered (MVC) or Identity Server Separated (Angular): yes Public website: yes
Running in locally with Null Email Sender in use.
The issue arises in the following scenario:
- Navigate to the web public page
- Click Login (navigates to Identity server)
- Click Forgot password
- Enter email for password reset
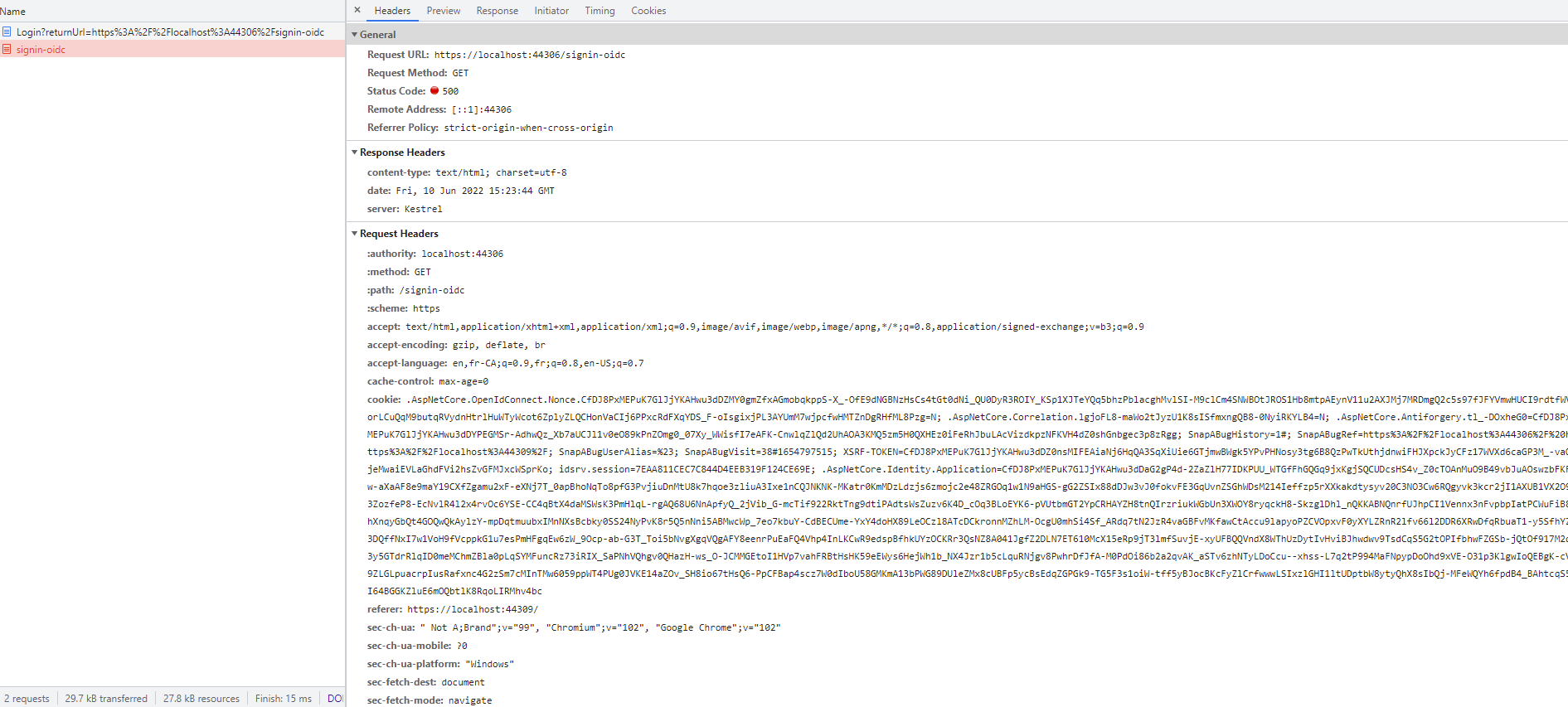
- Copy & paste the password reset link from the Identity Server log into browser (ie. https://localhost:44349/Account/ResetPassword?userId=bcece16c-6098-6c0c-1ad3-3a045aecf37c&__tenant=&resetToken=CfDJ8PxMEPuK7GlJjYKAHwu3dDapqpsWhVzKFziM6xXtptAvMFgXVCOc%2BIIWnBiY1Uq0GDOOmno4yc99Ur26Zu4GCQPTDDino5Ix8dGgf6meYEtyXo%2FpH0VQlhB3C%2F0Rhy6h0lfn6lFkXK0yqHQGjTIB22xWUfYlzljkJDmCc%2FFy%2BuOR5PV8sMSKOvkUPz6T0bwUUCtrg1qRgKgL5l%2FeUWdijBcffVip%2B1nRPJ2ijhnVqS0j&returnUrl=https://localhost:44306/signin-oidc)
- On Reset Password page, enter new password
- On Reset Pasword Confirmation page, press Go to the application
- On Login page, enter credentials and Login.
- System redirects to the Identity Server page (even though the return url in the password reset is to the public website "https://localhost:44306/signin-oidc")
As a result of this issue, we had added a redirect setting (https://localhost:44306) in the appsettings for the identity server project:
"RedirectAllowedUrls": "http://localhost:4200,https://localhost:44307,https://localhost:44306"
When the redirect url is added, the exception described above is thrown (RemoteAuthentication: OpenIdConnectAuthenticationHandler: message.State is null or empty.).
We also tried with the RedirectAllowedUrl of "https://localhost:44306/signin-oidc" with the same result.