After upgrading from IdentityServer to OpenIdDict, to generate the token I am getting below scope is invalid error.
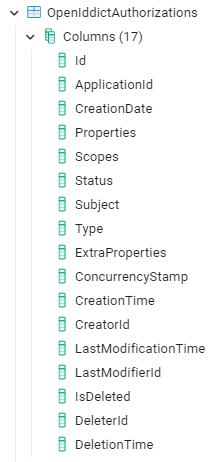
Old App - IdentityServerApiResourceScopes table have only two columns - ApiResourceId, Scope, but similar table from OpenIdDict is expecting too many columns as below.
is there any mechanism to migrating data from Identity server tables to opendict tables?
Note: We can't use db migrations at this time.
Check the docs before asking a question: https://docs.abp.io/en/commercial/latest/ Check the samples, to see the basic tasks: https://docs.abp.io/en/commercial/latest/samples/index The exact solution to your question may have been answered before, please use the search on the homepage.
If you're creating a bug/problem report, please include followings:
- ABP Framework version: vX.X.X
- UI type: Angular / MVC / Blazor
- DB provider: EF Core / MongoDB
- Tiered (MVC) or Identity Server Separated (Angular): yes / no
- Exception message and stack trace:
- Steps to reproduce the issue:"
17 Answer(s)
-
0
HI
You can migrator a new database and then check the tables of OpenIddict.
You need to add all scope names in postman.
-
0
HI
You can migrator a new database and then check the tables of OpenIddict.
You need to add all scope names in postman.
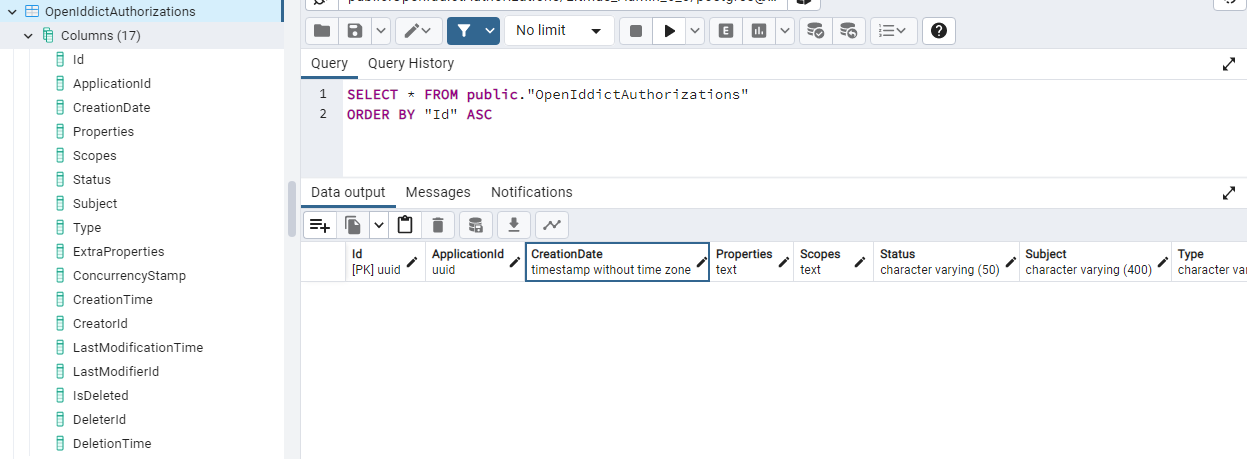
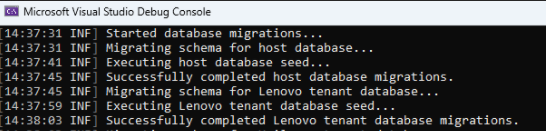
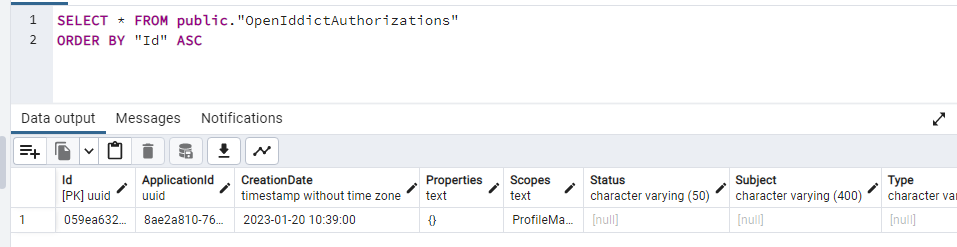
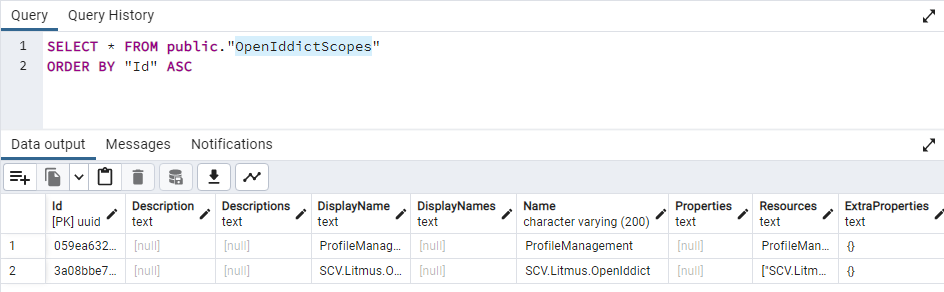
Using DbMigrator only I have done the migration successfully (its showing tenant db seed also done successfully, but it didn't), see the below screen shot for the same, but the OpenIdDict related table is empty.
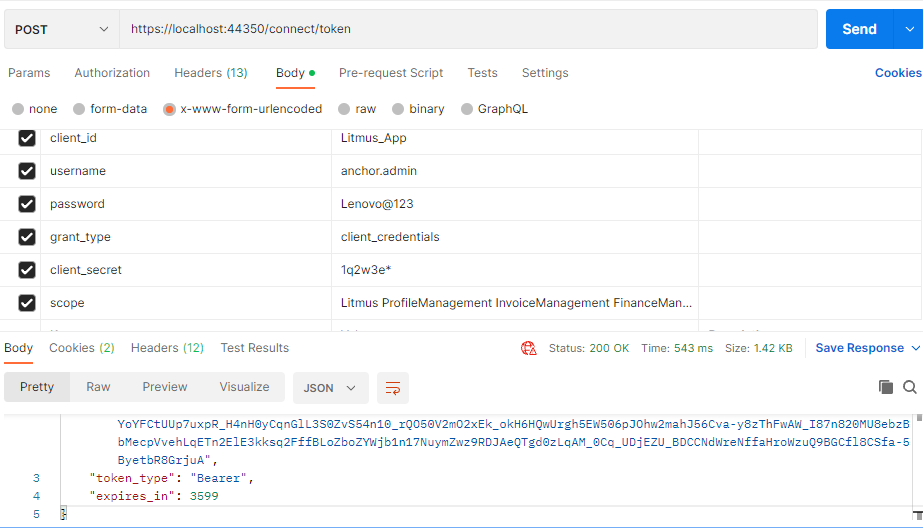
I have added all scope names in postman see below screen shot (in last screen shot I think its minimized)
Could you please let me know how to seed data from Identity Server tables (baked up) to OpenIdDict tables?
-
0
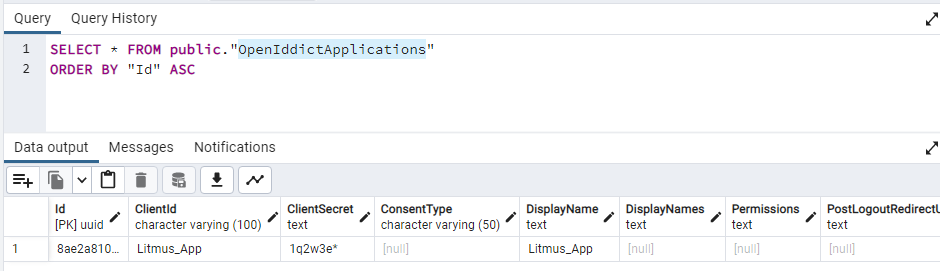
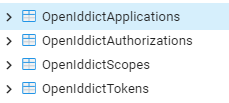
The client(application) stores at
OpenIddictApplicationstables.Please check the logs to see the details error of
invalid_client -
0
The client(application) stores at
OpenIddictApplicationstables.Please check the logs to see the details error of
invalid_clientI have added the required values in the below tables.
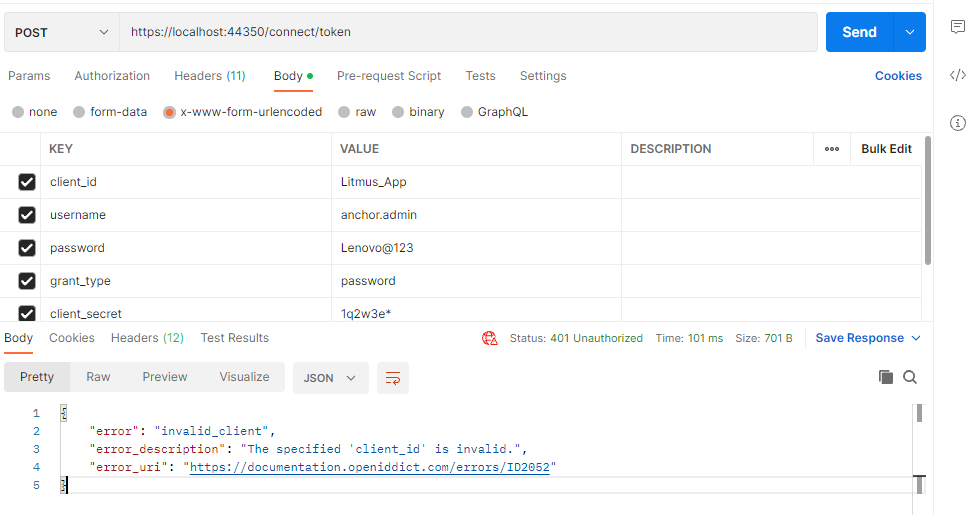
but when I post the token request from Postman, I am getting the below error, 1. Could you please tell me what could be the issue? 2. Is dbmigrator will collect the data from IdentityServer tables and push in to OpenIdDict tables (Schema + Data)?
-
0
- Could you please tell me what could be the issue?
- Is dbmigrator will collect the data from IdentityServer tables and push in to OpenIdDict tables (Schema + Data)?
dbmigrator will only create Scopes and Applications in the template. they come from https://github.com/abpframework/abp/blob/dev/templates/app/aspnet-core/src/MyCompanyName.MyProjectName.DbMigrator/appsettings.json#L5
So you can change the
appsettings.jsonand reseed your client from the identity server. -
0
- Could you please tell me what could be the issue?
- Is dbmigrator will collect the data from IdentityServer tables and push in to OpenIdDict tables (Schema + Data)?
dbmigrator will only create Scopes and Applications in the template. they come from https://github.com/abpframework/abp/blob/dev/templates/app/aspnet-core/src/MyCompanyName.MyProjectName.DbMigrator/appsettings.json#L5
So you can change the
appsettings.jsonand reseed your client from the identity server.how can the data be imported from Identity tables to OpenIddict tables without migration?
-
0
how can the data be imported from Identity tables to OpenIddict tables without migration?
There is currently no way to do this.
-
0
how can the data be imported from Identity tables to OpenIddict tables without migration?
There is currently no way to do this.
1. Could you please provide the sample data (at least one entry with relations ) for below all tables or first 3 tables?
2. While I am sending token api post request from postman, I am getting below error, what could be the issue for this? System.NullReferenceException: Object reference not set to an instance of an object. at Volo.Abp.OpenIddict.Applications.OpenIddictApplicationExtensions.ToModel(OpenIddictApplication entity) at Volo.Abp.OpenIddict.Applications.AbpOpenIddictApplicationStore.FindByClientIdAsync(String identifier, CancellationToken cancellationToken) at Volo.Abp.OpenIddict.Applications.AbpOpenIddictApplicationCache.<>c__DisplayClass2_0.<<FindByClientIdAsync>b__0>d.MoveNext() --- End of stack trace from previous location --- at Volo.Abp.Caching.DistributedCache
2.GetOrAddAsync(TCacheKey key, Func1 factory, Func1 optionsFactory, Nullable1 hideErrors, Boolean considerUow, CancellationToken token) at Volo.Abp.OpenIddict.Applications.AbpOpenIddictApplicationCache.FindByClientIdAsync(String identifier, CancellationToken cancellationToken) at OpenIddict.Core.OpenIddictApplicationManager1.FindByClientIdAsync(String identifier, CancellationToken cancellationToken) at OpenIddict.Core.OpenIddictApplicationManager1.OpenIddict.Abstractions.IOpenIddictApplicationManager.FindByClientIdAsync(String identifier, CancellationToken cancellationToken) at OpenIddict.Server.OpenIddictServerHandlers.Exchange.ValidateClientId.HandleAsync(ValidateTokenRequestContext context) at OpenIddict.Server.OpenIddictServerDispatcher.DispatchAsync[TContext](TContext context) at OpenIddict.Server.OpenIddictServerDispatcher.DispatchAsync[TContext](TContext context) at OpenIddict.Server.OpenIddictServerHandlers.Exchange.ValidateTokenRequest.HandleAsync(ProcessRequestContext context) at OpenIddict.Server.OpenIddictServerDispatcher.DispatchAsync[TContext](TContext context) at OpenIddict.Server.OpenIddictServerDispatcher.DispatchAsync[TContext](TContext context) at OpenIddict.Server.AspNetCore.OpenIddictServerAspNetCoreHandler.HandleRequestAsync() at Microsoft.AspNetCore.Authentication.AuthenticationMiddleware.Invoke(HttpContext context) at SCV.Litmus.Shared.DecryptHttpHeadersMiddleware.InvokeAsync(HttpContext context, RequestDelegate next) in C:\ABP Upgrade_6\SCV.Litmus\aspnet-core\shared\SCV.Litmus.Shared\Middleware\DecryptHttpHeadersMiddleware.cs:line 50 at Microsoft.AspNetCore.Builder.UseMiddlewareExtensions.<>c__DisplayClass6_1.<<UseMiddlewareInterface>b__1>d.MoveNext() --- End of stack trace from previous location --- at SCV.Litmus.Shared.DecryptHttpRequestMiddleware.InvokeAsync(HttpContext context, RequestDelegate next) in C:\ABP Upgrade_6\SCV.Litmus\aspnet-core\shared\SCV.Litmus.Shared\Middleware\DecryptHttpRequestMiddleware.cs:line 101 at Microsoft.AspNetCore.Builder.UseMiddlewareExtensions.<>c__DisplayClass6_1.<<UseMiddlewareInterface>b__1>d.MoveNext() --- End of stack trace from previous location --- at Volo.Abp.AspNetCore.Tracing.AbpCorrelationIdMiddleware.InvokeAsync(HttpContext context, RequestDelegate next) at Microsoft.AspNetCore.Builder.UseMiddlewareExtensions.<>c__DisplayClass6_1.<<UseMiddlewareInterface>b__1>d.MoveNext() --- End of stack trace from previous location --- at SCV.Litmus.LitmusIdentityServerModule.<>c.<<OnApplicationInitialization>b__3_1>d.MoveNext() in C:\ABP Upgrade_6\SCV.Litmus\aspnet-core\microservices\SCV.Litmus.IdentityServer\LitmusIdentityServerModule.cs:line 183 --- End of stack trace from previous location --- at Microsoft.AspNetCore.Localization.RequestLocalizationMiddleware.Invoke(HttpContext context) at Microsoft.AspNetCore.RequestLocalization.AbpRequestLocalizationMiddleware.InvokeAsync(HttpContext context, RequestDelegate next) at Microsoft.AspNetCore.Builder.UseMiddlewareExtensions.<>c__DisplayClass6_1.<<UseMiddlewareInterface>b__1>d.MoveNext() --- End of stack trace from previous location --- at Microsoft.AspNetCore.Diagnostics.DeveloperExceptionPageMiddleware.Invoke(HttpContext context)HEADERS
Accept: / Accept-Encoding: gzip, deflate, br Connection: keep-alive Content-Length: 132 Content-Type: application/x-www-form-urlencoded Host: localhost:44350 User-Agent: PostmanRuntime/7.29.2 __tenant: d1be844b-d3a2-031a-f036-39f5d4380239 Postman-Token: 9c42e329-4d30-40f8-82bc-db0704106cc2 X-Correlation-Id: d2e19d4a624240d0aeab51f8b6a33466
-
0
hi
You can create a new project and migrator it to a new database and then check the tables of OpenIddict.
The data come from the
OpenIddictDataSeedContributorof your projecthttps://github.com/abpframework/abp/blob/dev/templates/app/aspnet-core/src/MyCompanyName.MyProjectName.Domain/OpenIddict/OpenIddictDataSeedContributor.cs
-
0
hi
You can create a new project and migrator it to a new database and then check the tables of OpenIddict.
The data come from the
OpenIddictDataSeedContributorof your projecthttps://github.com/abpframework/abp/blob/dev/templates/app/aspnet-core/src/MyCompanyName.MyProjectName.Domain/OpenIddict/OpenIddictDataSeedContributor.cs
-
0
openiddict has nothing to do with the database, you can create a 6.x template project with postgress
abp new BookStore -t app-pro -v 6.0.3 --dbms PostgreSQL -
0
openiddict has nothing to do with the database, you can create a 6.x template project with postgress
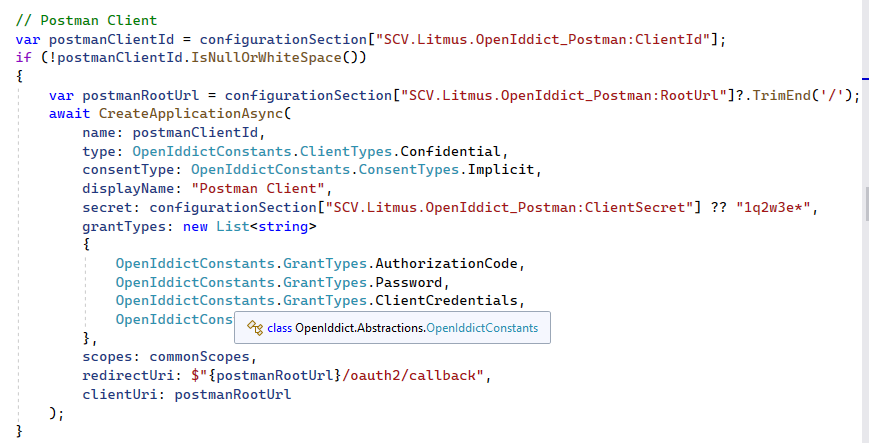
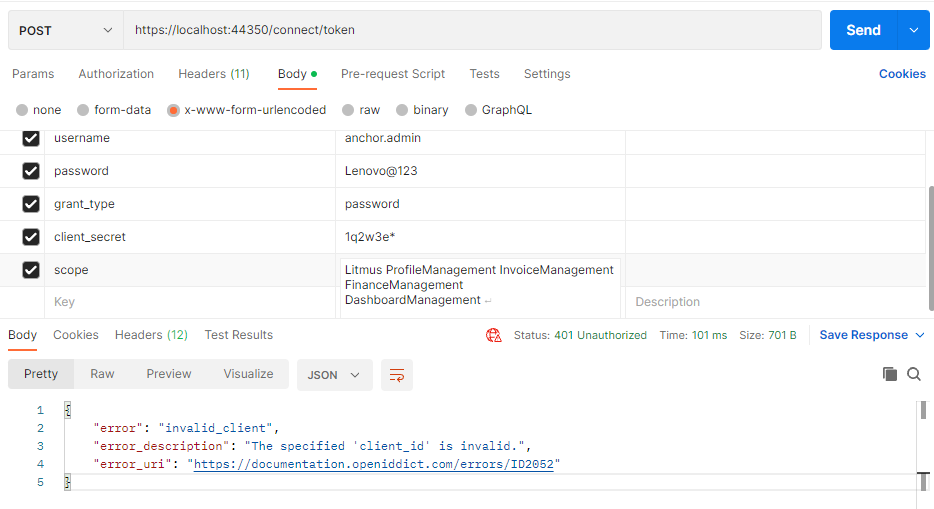
abp new BookStore -t app-pro -v 6.0.3 --dbms PostgreSQL**While sending token generation request, I am getting the following "The specified client credentials are invalid." error message **from Postman client.
 tried grant_type for password & client_credentials also, but this error is coming.
tried grant_type for password & client_credentials also, but this error is coming.Note: 1. AbpUsers table contains the user details in both the databases, ie Host & Tenant. 2. Logs doesn't contain any details about this error.
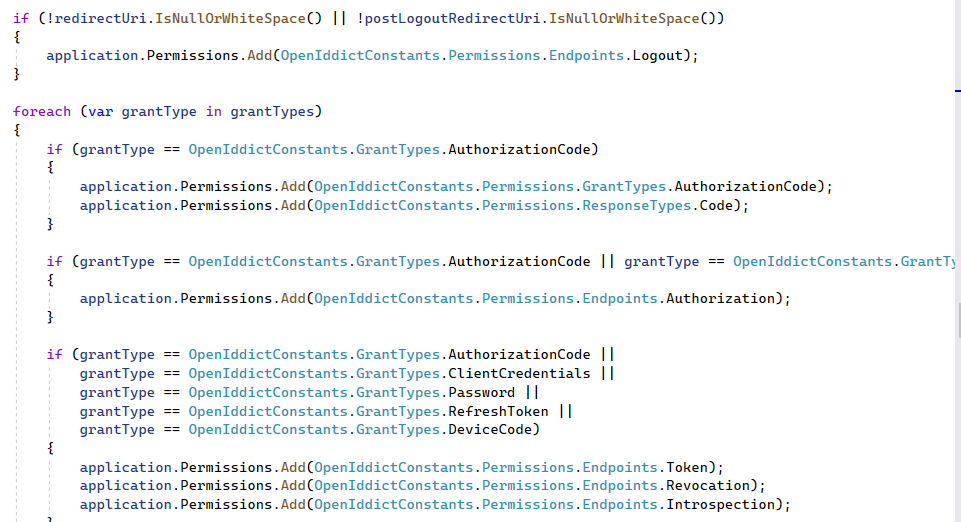
Permissions Column have following data. ["rst:code id_token","ept:logout","gt:authorization_code","rst:code","ept:authorization","ept:token","ept:revocation","ept:introspection","gt:implicit","rst:id_token","scp:address","scp:email","scp:phone","scp:profile","scp:roles","scp:Litmus_Admin_6_0"]
Could you please tell the reason for the error "The specified client credentials are invalid." and guide us to resolve this.
-
0
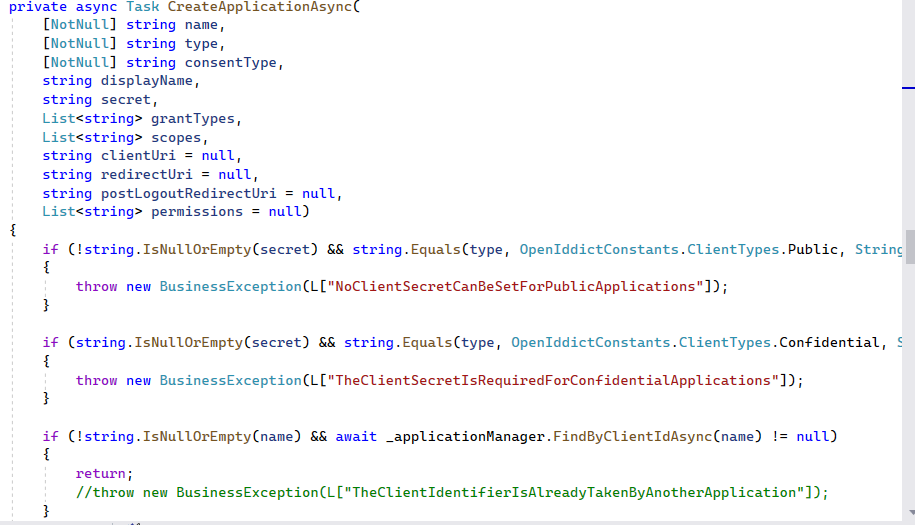
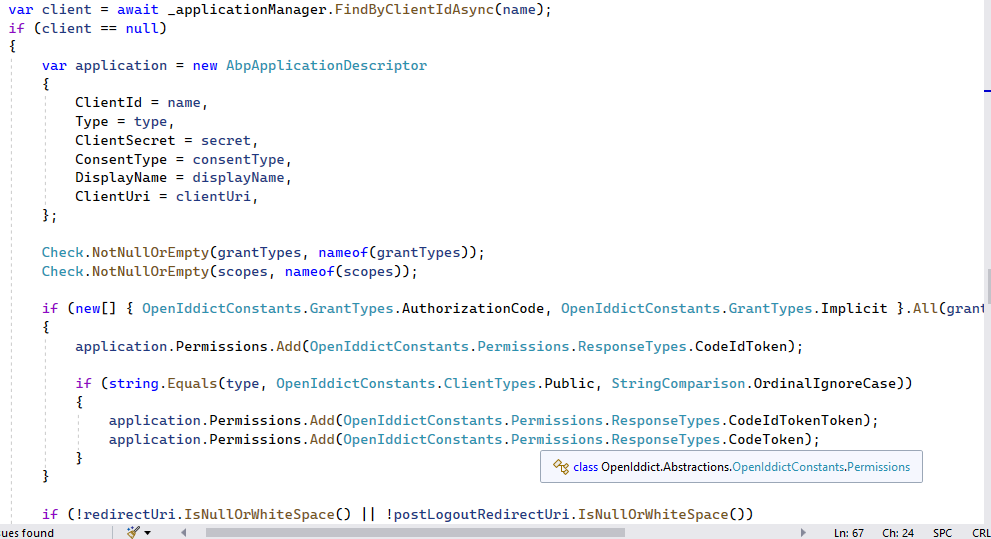
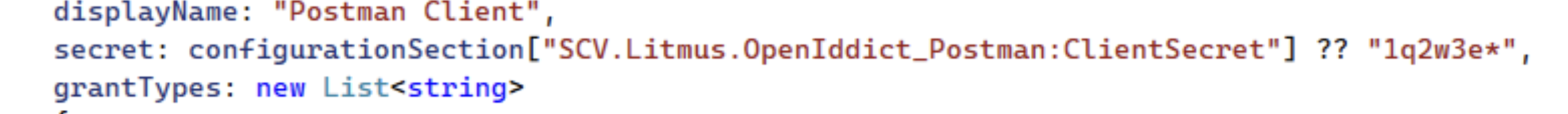
What's the client info of
Litmus_App?You can share the create code. eg
await CreateApplicationAsync( name: blazorServerTieredClientId!, type: OpenIddictConstants.ClientTypes.Confidential, consentType: OpenIddictConstants.ConsentTypes.Implicit, displayName: "Blazor Server Application", secret: configurationSection["MyProjectName_BlazorServerTiered:ClientSecret"] ?? "1q2w3e*", grantTypes: new List<string> //Hybrid flow { OpenIddictConstants.GrantTypes.AuthorizationCode, OpenIddictConstants.GrantTypes.Implicit }, scopes: commonScopes, redirectUri: $"{blazorServerTieredRootUrl}signin-oidc", clientUri: blazorServerTieredRootUrl, postLogoutRedirectUri: $"{blazorServerTieredRootUrl}signout-callback-oidc" );Logs doesn't contain any details about this error.
Please share the request logs.
-
0
Request Collection { "info": { "_postman_id": "b970efa1-47f1-4868-9316-c3e101952ad1", "name": "Dormancy-LastLoginDate", "schema": "https://schema.getpostman.com/json/collection/v2.1.0/collection.json", "_exporter_id": "13713657" }, "item": [ { "name": "Token", "event": [ { "listen": "prerequest", "script": { "exec": [ "" ], "type": "text/javascript" } } ], "protocolProfileBehavior": { "disabledSystemHeaders": {} }, "request": { "auth": { "type": "noauth" }, "method": "POST", "header": [ { "key": "__tenant", "value": "d1be844b-d3a2-031a-f036-39f5d4380239", "type": "text" }, { "key": "__tenant", "value": "3a036d5d-4a75-6653-9ea7-45b4fbd30bd4", "type": "default", "disabled": true }, { "key": "authenticationCode", "value": "423260", "type": "text", "disabled": true } ], "body": { "mode": "urlencoded", "urlencoded": [ { "key": "client_id", "value": "Litmus_App", "type": "text" }, { "key": "username", "value": "anchor.admin", "type": "text" }, { "key": "password", "value": "Lenovo@123", "type": "text" }, { "key": "grant_type", "value": "password", "type": "text" }, { "key": "client_secret", "value": "1q2w3e*", "type": "text" }, { "key": "scope", "value": "Litmus ProfileManagement InvoiceManagement FinanceManagement DashboardManagement", "type": "text" } ] }, "url": { "raw": "https://localhost:44350/connect/token", "protocol": "https", "host": [ "localhost" ], "port": "44350", "path": [ "connect", "token" ] } }, "response": [] }, { "name": "SendSuspensionAndDeactivationReminderNotification", "request": { "auth": { "type": "bearer", "bearer": [ { "key": "token", "value": "{{token}}", "type": "string" } ] }, "method": "POST", "header": [ { "key": "__tenant", "value": "d1be844b-d3a2-031a-f036-39f5d4380239", "type": "text" } ], "url": { "raw": "https://localhost:44398/profile/api/ProfileManagement/AccountNotifications/sendSuspensionAndDeactivationReminderNotification?rolesType=1", "protocol": "https", "host": [ "localhost" ], "port": "44398", "path": [ "profile", "api", "ProfileManagement", "AccountNotifications", "sendSuspensionAndDeactivationReminderNotification" ], "query": [ { "key": "rolesType", "value": "1" } ] } }, "response": [] } ], "auth": { "type": "bearer", "bearer": [ { "key": "token", "value": "{{token}}", "type": "string" } ] }, "event": [ { "listen": "prerequest", "script": { "type": "text/javascript", "exec": [ "" ] } }, { "listen": "test", "script": { "type": "text/javascript", "exec": [ "" ] } } ] } -
0
-
0
-
0
I think the scope will be in the access_token, you can check the claims info.
https://jwt.io/